Employee Leave Management System Capstone Project Document
Introduction
This project is aimed at developing a web based Leave Management Tool, which is of importance to either an organization or a college.
The Leave Management system is an Intranet based application that can be accessed throughout the organization or a specified group/Dept. This system can be used to automate the workflow of leave applications and their approvals. The periodic crediting of leave is also automated. There are features like notifications, cancellation of leave, automatic approval of leave, report generators etc in this Tool.
This project is aimed at developing a web based Leave Management Tool, which is of importance to either an organization or a college.
The Easy Leave is an Intranet based application that can be accessed throughout the organization or a specified group/Dept. This system can be used to automate the workflow of leave applications and their approvals. The periodic crediting of leave is also automated. There are features like notifications, cancellation of leave, automatic approval of leave, report generators etc in this Tool.
Functional components of the project:
There are registered people in the system. Some are approvers. An approver can also be a requestor. In an organization, the hierarchy could be Engineers/Managers/Business Managers/Managing Director etc. In a college, it could be Lecturer/Professor/Head of the Department/Dean/Principal etc.
Following is a list of functionalities of the system:
- A person should be able to
- login to the system through the first page of the application
- change the password after logging into the system
- see his/her eligibility details (like how many days of leave he/she is eligible for etc)
- query the leave balance
- see his/her leave history since the time he/she joined the company/college
- apply for leave, specifying the from and to dates, reason for taking leave, address for communication while on leave and his/her superior’s email id
- see his/her current leave applications and the leave applications that are submitted to him/her for approval or cancellation
- approve/reject the leave applications that are submitted to him/her
- withdraw his/her leave application (which has not been approved yet)
- Cancel his/her leave (which has been already approved). This will need to be approved by his/her Superior
- get help about the leave system on how to use the different features of the system
As soon as a leave application /cancellation request /withdrawal /approval /rejection /password-change is made by the person, an automatic email should be sent to the person and his superior giving details about the action
The number of days of leave (as per the assumed leave policy) should be automatically credited to everybody and a notification regarding the same be sent to them automatically
An automatic leave-approval facility for leave applications which are older than 2 weeks should be there. Notification about the automatic leave approval should be sent to the person as well as his superior
Existing System:
- All Work are done Manually.
- Cannot Upload and Download the latest updates.
- No use of Web Services and Remoting.
- Risk of mismanagement and of data when the project is under development.
- Less Security.
- No proper coordination between different Applications and Users.
- Fewer Users – Friendly.
Proposed System:
The development of the new system contains the following activities, which try to automate the entire process keeping in view of the database integration approach.
- User friendliness is provided in the application with various controls.
- The system makes the overall project management much easier and flexible.
- Readily upload the latest updates, allows user to download the alerts by clicking the URL.
- There is no risk of data mismanagement at any level while the project development is under process.
Study Of The System
To provide flexibility to the users, the interfaces have been developed that are accessible through a browser. The GUI’S at the top level have been categorized as
- Administrative user interface
- The operational or generic user interface
The ‘administrative user interface’ concentrates on the consistent information that is practically, part of the organizational activities and which needs proper authentication for the data collection. These interfaces help the administrators with all the transactional states like Data insertion, Data deletion and Date updation along with the extensive data search capabilities.
The ‘operational or generic user interface’ helps the end users of the system in transactions through the existing data and required services. The operational user interface also helps the ordinary users in managing their own information in a customized manner as per the included flexibilities
Input & Outpout Representetion
Input design is a part of overall system design. The main objective during the input design is as given below:
- To produce a cost-effective method of input.
- To achieve the highest possible level of accuracy.
- To ensure that the input is acceptable and understood by the user.
INPUT STAGES:
The main input stages can be listed as below:
- Data recording
- Data transcription
- Data conversion
- Data verification
- Data control
- Data transmission
- Data validation
- Data correction
INPUT TYPES:
It is necessary to determine the various types of inputs. Inputs can be categorized as follows:
- External inputs, which are prime inputs for the system.
- Internal inputs, which are user communications with the system.
- Operational, which are computer department’s communications to the system?
- Interactive, which are inputs entered during a dialogue.
INPUT MEDIA:
At this stage choice has to be made about the input media. To conclude about the input media consideration has to be given to;
- Type of input
- Flexibility of format
- Speed
- Accuracy
- Verification methods
- Rejection rates
- Ease of correction
- Storage and handling requirements
- Security
- Easy to use
- Portability
Keeping in view the above description of the input types and input media, it can be said that most of the inputs are of the form of internal and interactive. As
Input data is to be the directly keyed in by the user, the keyboard can be considered to be the most suitable input device.
OUTPUT DESIGN:
In general are:
- External Outputs whose destination is outside the organization.
- Internal Outputs whose destination is with in organization and they are the User’s main interface with the computer. Outputs from computer systems are required primarily to communicate the results of processing to users. They are also used to provide a permanent copy of the results for later consultation. The various types of outputs
- Operational outputs whose use is purely with in the computer department.
- Interface outputs, which involve the user in communicating directly with the system.
OUTPUT DEFINITION
The outputs should be defined in terms of the following points:
- Type of the output
- Content of the output
- Format of the output
- Location of the output
- Frequency of the output
- Volume of the output
- Sequence of the output
It is not always desirable to print or display data as it is held on a computer. It should be decided as which form of the output is the most suitable.
For Example
Will decimal points need to be inserted
Should leading zeros be suppressed.
OUTPUT MEDIA:
In the next stage it is to be decided that which medium is the most appropriate for the output. The main considerations when deciding about the output media are:
- The suitability for the device to the particular application.
- The need for a hard copy.
- The response time required.
- The location of the users
- The software and hardware available.
Keeping in view the above description the project is to have outputs mainly coming under the category of internal outputs. The main outputs desired according to the requirement specification are:
The outputs were needed to be generated as a hard copy and as well as queries to be viewed on the screen. Keeping in view these outputs, the format for the output is taken from the outputs, which are currently being obtained after manual processing. The standard printer is to be used as output media for hard copies.
Process Model Used With Justification
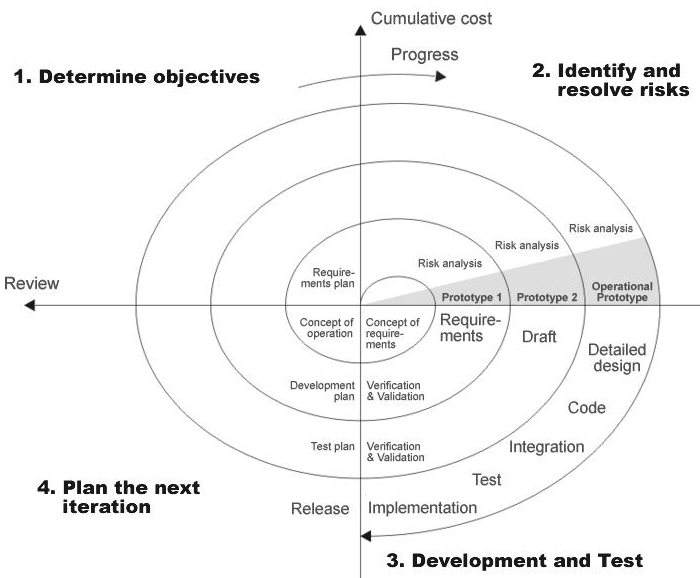
SDLC (Spiral Model):
SDLC is nothing but Software Development Life Cycle. It is a standard which is used by software industry to develop good software.
Stages in SDLC:
- Requirement Gathering
- Analysis
- Designing
- Coding
- Testing
- Maintenance
Requirements Gathering stage:
The requirements gathering process takes as its input the goals identified in the high-level requirements section of the project plan. Each goal will be refined into a set of one or more requirements. These requirements define the major functions of the intended application, define
operational data areas and reference data areas, and define the initial data entities. Major functions include critical processes to be managed, as well as mission critical inputs, outputs and reports. A user class hierarchy is developed and associated with these major functions, data areas, and data entities. Each of these definitions is termed a Requirement. Requirements are identified by unique requirement identifiers and, at minimum, contain a requirement title and textual description.
These requirements are fully described in the primary deliverables for this stage: the Requirements Document and the Requirements Traceability Matrix (RTM). The requirements document contains complete descriptions of each requirement, including diagrams and references to external documents as necessary. Note that detailed listings of database tables and fields are not included in the requirements document.
The title of each requirement is also placed into the first version of the RTM, along with the title of each goal from the project plan. The purpose of the RTM is to show that the product components developed during each stage of the software development lifecycle are formally connected to the components developed in prior stages.
In the requirements stage, the RTM consists of a list of high-level requirements, or goals, by title, with a listing of associated requirements for each goal, listed by requirement title. In this hierarchical listing, the RTM shows that each requirement developed during this stage is formally linked to a specific product goal. In this format, each requirement can be traced to a specific product goal, hence the term requirements traceability.
The outputs of the requirements definition stage include the requirements document, the RTM, and an updated project plan.
- Feasibility study is all about identification of problems in a project.
- of staff required to handle a project is represented as Team Formation, in this case only modules are individual tasks will be assigned to employees who are working for that project.
- Project Specifications are all about representing of various possible inputs submitting to the server and corresponding outputs along with reports maintained by administrator
Analysis Stage:
The planning stage establishes a bird’s eye view of the intended software product, and uses this to establish the basic project structure, evaluate feasibility and risks associated with the project, and describe appropriate management and technical approaches.
The most critical section of the project plan is a listing of high-level product requirements, also referred to as goals. All of the software product requirements to be developed during the requirements definition stage flow from one or more of these goals. The minimum information for each goal consists of a title and textual description, although additional information and references to external documents may be included. The outputs of the project planning stage are the configuration management plan, the quality assurance plan, and the project plan and schedule, with a detailed listing of scheduled activities for the upcoming Requirements stage, and high level estimates of effort for the out stages.
Designing Stage:
The design stage takes as its initial input the requirements identified in the approved requirements document. For each requirement, a set of one or more design elements will be produced as a result of interviews, workshops, and/or prototype efforts. Design elements describe the desired software features in detail, and generally include functional hierarchy diagrams, screen layout diagrams, tables of business rules, business process diagrams, pseudo code, and a complete entity-relationship diagram with a full data dictionary. These design elements are intended to describe the software in sufficient detail that skilled programmers may develop the software with minimal additional input.
When the design document is finalized and accepted, the RTM is updated to show that each design element is formally associated with a specific requirement. The outputs of the design stage are the design document, an updated RTM, and an updated project plan.
Development (Coding) Stage:
The development stage takes as its primary input the design elements described in the approved design document. For each design element, a set of one or more software artifacts will be produced. Software artifacts include but are not limited to menus, dialogs, data management forms, data reporting formats, and specialized procedures and functions. Appropriate test cases will be developed for each set of functionally related software artifacts, and an online help system will be developed to guide users in their interactions with the software.
The RTM will be updated to show that each developed artifact is linked to a specific design element, and that each developed artifact has one or more corresponding test case items. At this point, the RTM is in its final configuration. The outputs of the development stage include a fully functional set of software that satisfies the requirements and design elements previously documented, an online help system that describes the operation of the software, an implementation map that identifies the primary code entry points for all major system functions, a test plan that describes the test cases to be used to validate the correctness and completeness of the software, an updated RTM, and an updated project plan.
Integration & Test Stage:
During the integration and test stage, the software artifacts, online help, and test data are migrated from the development environment to a separate test environment. At this point, all test cases are run to verify the correctness and completeness of the software. Successful execution of the test suite confirms a robust and complete migration capability. During this stage, reference data is finalized for production use and production users are identified and linked to their appropriate roles. The final reference data (or links to reference data source files) and production user list are compiled into the Production Initiation Plan.
The outputs of the integration and test stage include an integrated set of software, an online help system, an implementation map, a production initiation plan that describes reference data and production users, an acceptance plan which contains the final suite of test cases, and an updated project plan.
- Installation & Acceptance Test:
During the installation and acceptance stage, the software artifacts, online help, and initial production data are loaded onto the production server. At this point, all test cases are run to verify the correctness and completeness of the software. Successful execution of the test suite is a prerequisite to acceptance of the software by the customer.
After customer personnel have verified that the initial production data load is correct and the test suite has been executed with satisfactory results, the customer formally accepts the delivery of the software.
The primary outputs of the installation and acceptance stage include a production application, a completed acceptance test suite, and a memorandum of customer acceptance of the software. Finally, the PDR enters the last of the actual labor data into the project schedule and locks the project as a permanent project record. At this point the PDR “locks” the project by archiving all software items, the implementation map, the source code, and the documentation for future reference.
Maintenance:
Outer rectangle represents maintenance of a project, Maintenance team will start with requirement study, understanding of documentation later employees will be assigned work and they will under go training on that particular assigned category.
For this life cycle there is no end, it will be continued so on like an umbrella (no ending point to umbrella sticks).
Feasibility Study
Preliminary investigation examines project feasibility; the likelihood the system will be useful to the organization. The main objective of the feasibility study is to test the Technical, Operational and Economical feasibility for adding new modules and debugging old running system. All systems are feasible if they are given unlimited resources and infinite time. There are aspects in the feasibility study portion of the preliminary investigation:
- Technical Feasibility
- Operation Feasibility
- Economical Feasibility
TECHNICAL FEASIBILITY
The technical issue usually raised during the feasibility stage of the investigation includes the following:
- Does the necessary technology exist to do what is suggested?
- Do the proposed equipments have the technical capacity to hold the data required to use the new system?
- Will the proposed system provide adequate response to inquiries, regardless of the number or location of users?
- Can the system be upgraded if developed?
- Are there technical guarantees of accuracy, reliability, ease of access and data security?
OPERATIONAL FEASIBILITY
OPERATIONAL FEASIBILITY
User-friendly
Customer will use the forms for their various transactions i.e. for adding new routes, viewing the routes details. Also the Customer wants the reports to view the various transactions based on the constraints. Theses forms and reports are generated as user-friendly to the Client.
Reliability
The package wills pick-up current transactions on line. Regarding the old transactions, User will enter them in to the system.
Security
The web server and database server should be protected from hacking, virus etc
Portability
The application will be developed using standard open source software (Except Oracle) like Java, tomcat web server, Internet Explorer Browser etc these software will work both on Windows and Linux o/s. Hence portability problems will not arise.
Availability
This software will be available always.
Maintainability
The system called the ewheelz uses the 2-tier architecture. The 1st tier is the GUI, which is said to be front-end and the 2nd tier is the database, which uses My-Sql, which is the back-end.
The front-end can be run on different systems (clients). The database will be running at the server. Users access these forms by using the user-ids and the passwords.
3.3 ECONOMIC FEASILITY
The computerized system takes care of the present existing system’s data flow and procedures completely and should generate all the reports of the manual system besides a host of other management reports.
It should be built as a web based application with separate web server and database server. This is required as the activities are spread through out the organization customer wants a centralized database. Further some of the linked transactions take place in different locations.
Open source software like TOMCAT, JAVA, Mysql and Linux is used to minimize the cost for the Customer.
Requirements Specifications
FUNCTIONAL REQUIREMENTS SPECIFICATION
This application consists following modules.
MODULES
Administration
Employee
Search
Report
Authentication
MODULE DESCRIPTION
Administrator:-
In this module the Administrator has the privileges to add all the Employees and register them in the organization and check the information of the Employee and check the status of the leave when they have taken and what type of leave they have taken and search is done based on the employee and report is generated based on employee.
Search:-
This module contain complete search like Leave search, Type of Leave, Employee based on the leave and starting and ending day of leave.
Employee:-
In this module employee has the privileges to use his username and password for login and he can see the request given by the customer and he can pass the process to the Business Manager and maintain the record of the customers.
Reports:-
This module contains all the information about the reports generated by the Employees based on the Performance and by the leave status.
Authentication:-
This module contains all the information about the authenticated user. User without his username and password can’t enter into the login if he is only the authenticated user then he can enter to his login.
PERFORMANCE REQUIREMENTS
Performance is measured in terms of the output provided by the application. Requirement specification plays an important part in the analysis of a system. Only when the requirement specifications are properly given, it is possible to design a system, which will fit into required environment. It rests largely with the users of the existing system to give the requirement specifications because they are the people who finally use the system. This is because the requirements have to be known during the initial stages so that the system can be designed according to those requirements. It is very difficult to change the system once it has been designed and on the other hand designing a system, which does not cater to the requirements of the user, is of no use.
The requirement specification for any system can be broadly stated as given below:
- The system should be able to interface with the existing system
- The system should be accurate
- The system should be better than the existing system
The existing system is completely dependent on the user to perform all the duties.
SOFTWARE REQUIREMENTS:
One of the most difficult tasks is that, the selection of the software, once system requirement is known is determining whether a particular software package fits the requirements. After initial selection further security is needed to determine the desirability of particular software compared with other candidates. This section first summarizes the application requirement question and then suggests more detailed comparisons.
- Operating System ——– Windows 95/98/NT/2000
- Browser ——– IE
- Web/Application Server ——– apache web server
- Database Server ——– Mysql
- Database Connectivity ——– JDBC
- Other Tools & Technologies ——– PHP, HTML
HARDWARE REQUIREMENTS:
The selection of hardware is very important in the existence and proper working of any software. In the selection of hardware, the size and the capacity requirements are also important.
The Web Based Manufacturing System can be efficiently run on Pentium system with at least 128 MB RAM and Hard disk drive having 20 GB. Floppy disk drive of 1.44 MB and 14 inch Samsung color monitor suits the information system operation.(A Printer is required for hard copy output).
- Pentium processor ——– 233 MHZ or above
- RAM Capacity ——– 128MB
- Hard Disk ——– 20GB
- Floppy disk ——– 44 MB
- CD-ROM Drive ——– 32 HZ
- KEYBOARD ——– 108 Standard
INTRODUCTION TO PHP
PHP
PHP: Hypertext Preprocessor, is a widely used, general-purpose scripting language that was originally designed for web development, to produce dynamic web pages. It can be embedded into HTML and generally runs on a web server, which needs to be configured to process PHP code and create web page content from it. It can be deployed on most web servers and on almost every operating system and platform free of charge.
PHP was originally created by Rasmus Lerdorf in 1995 and has been in continuous development ever since. The main implementation of PHP is now produced by The PHP Group and serves as the de facto standard for PHP as there is no formal specification.PHP is free software released under the PHP License, which is incompatible with the GNU General Public License (GPL) because of restrictions on the use of the term PHP
PHP has evolved to include a command line interface capability and can also be used in standalone graphical applications.
USAGE
PHP is a general-purpose scripting language that is especially suited for web development. PHP generally runs on a web server. Any PHP code in a requested file is executed by the PHP runtime, usually to create dynamic web page content. It can also be used for command-line scripting and client-side GUI applications. PHP can be deployed on most web servers, many operating systems and platforms, and can be used with many relational database management systems. It is available free of charge, and the PHP Group provides the complete source code for users to build, customize and extend for their own use.
PHP primarily acts as a filter, taking input from a file or stream containing text and/or PHP instructions and outputs another stream of data; most commonly the output will be HTML. Since PHP 4, the PHP parser compiles input to produce byte code for processing by the Zend Engine, giving improved performance over its interpreter predecessor
Originally designed to create dynamic web pages, PHP now focuses mainly on server-side scripting, and it is similar to other server-side scripting languages that provide dynamic content from a web server to a client, such as Microsoft‘s Active Server Pages, Sun Microsystems‘ JavaServer Pages and mod_perl. PHP has also attracted the development of many frameworks that provide building blocks and a design structure to promote rapid application development (RAD). Some of these include CakePHP, Symfony, CodeIgniter, and Zend Framework, offering features similar to other web application frameworks.
About HTML
HTML, which stands for Hyper Text Markup Language, is the predominant markup language for web pages. It provides a means to create structured documents by denoting structural semantics for text such as headings, paragraphs, lists etc as well as for links, quotes, and other items. It allows images and objects to be embedded and can be used to create interactive forms. It is written in the form of HTML elements consisting of “tags” surrounded by angle brackets within the web page content. It can include or can load scripts in languages such as JavaScript which affect the behavior of HTML processors like Web browsers; and Cascading Style Sheets (CSS) to define the appearance and layout of text and other material. The W3C, maintainer of both HTML and CSS standards, encourages the use of CSS over explicit presentational markup.
Hyper Text Markup Language(HTML) is the encoding scheme used to create and format a web document. A user need not be an expert programmer to make use of HTML for creating hypertext documents that can be put on the internet.
Most graphical e-mail clients allow the use of a subset of HTML (often ill-defined) to provide formatting and semantic markup not available with plain text. This may include typographic information like coloured headings, emphasized and quoted text, inline images and diagrams. Many such clients include both a GUI editor for composing HTML e-mail messages and a rendering engine for displaying them. Use of HTML in e-mail is controversial because of compatibility issues, because it can help disguise phishing attacks, because it can confuse spam filters and because the message size is larger than plain text.
NAMING CONVENTIONS
The most common filename extension for files containing HTML is .html. A common abbreviation of this is .htm, which originated because some early operating systems and file systems, such as DOS and FAT, limited file extensions to three letters.
HTML APPLICATION
An HTML Application is a Microsoft Windows application that uses HTML and Dynamic HTML in a browser to provide the application’s graphical interface. A regular HTML file is confined to the security model of the web browser, communicating only to web servers and manipulating only webpage objects and site cookies. An HTA runs as a fully trusted application and therefore has more privileges, like creation/editing/removal of files and Windows Registry entries. Because they operate outside the browser’s security model, HTAs cannot be executed via HTTP, but must be downloaded (just like an EXE file) and executed from local file system
ABOUT JAVASCRIPT
JavaScript is an object-oriented scripting language used to enable programmatic access to objects within both the client application and other applications. It is primarily used in the form of client-side JavaScript, implemented as an integrated component of the web browser, allowing the development of enhanced user interfaces and dynamic websites. JavaScript is a dialect of the ECMAScript standard and is characterized as a dynamic, weakly typed, prototype-based language with first-class functions. JavaScript was influenced by many languages and was designed to look like Java, but to be easier for non-programmers to work with.
PROTOTYPE-BASED
JavaScript uses prototypes instead of classes for inheritance. It is possible to simulate many class-based features with prototypes in JavaScript.
Functions double as object constructors along with their typical role. Prefixing a function call with new creates a new object and calls that function with its local this keyword bound to that object for that invocation. The constructor’s prototype property determines the object used for the new object’s internal prototype. JavaScript’s built-in constructors, such as Array, also have prototypes that can be modified.
Unlike many object-oriented languages, there is no distinction between a function definition and a method definition. Rather, the distinction occurs during function calling; a function can be called as a method. When a function is called as a method of an object, the function’s local this keyword is bound to that object for that invocation.
USAGE
The primary use of JavaScript is to write functions that are embedded in or included from HTML pages and interact with the Document Object Model (DOM) of the page.
Because JavaScript code can run locally in a user’s browser (rather than on a remote server) it can respond to user actions quickly, making an application feel more responsive. Furthermore, JavaScript code can detect user actions which HTML alone cannot, such as individual keystrokes. Applications such as Gmail take advantage of this: much of the user-interface logic is written in JavaScript, and JavaScript dispatches requests for information (such as the content of an e-mail message) to the server. The wider trend of Ajax programming similarly exploits this strength.
A JavaScript engine (also known as JavaScript interpreter or JavaScript implementation) is an interpreter that interprets JavaScript source code and executes the script accordingly. The first JavaScript engine was created by Brendan Eich at Netscape Communications Corporation, for the Netscape Navigator web browser. A web browser is by far the most common host environment for JavaScript. Web browsers typically use the public API to create “host objects” responsible for reflecting the DOM into JavaScript.
4.3 MySQL:
Overview of the MySQL Database Management System
What is MySQL?
MySQL, the most popular Open Source SQL database management system, is developed, distributed, and supported by Oracle Corporation.
The MySQL Web site (http://www.mysql.com/) provides the latest information about MySQL software.
- MySQL is a database management system.
A database is a structured collection of data. It may be anything from a simple shopping list to a picture gallery or the vast amounts of information in a corporate network. To add, access, and process data stored in a computer database, you need a database management system such as MySQL Server. Since computers are very good at handling large amounts of data, database management systems play a central role in computing, as standalone utilities, or as parts of other applications.
- MySQL databases are relational
A relational database stores data in separate tables rather than putting all the data in one big storeroom. The database structures are organized into physical files optimized for speed. The logical model, with objects such as databases, tables, views, rows, and columns, offers a flexible programming environment. You set up rules governing the relationships between different data fields, such as one-to-one, one-to-many, unique, required or optional, and “pointers” between different tables. The database enforces these rules, so that with a well-designed database, your application never sees inconsistent, duplicate, orphan, out-of-date, or missing data.
The SQL part of “MySQL” stands for “Structured Query Language”. SQL is the most common standardized language used to access databases. Depending on your programming environment, you might enter SQL directly (for example, to generate reports), embed SQL statements into code written in another language, or use a language-specific API that hides the SQL syntax.
SQL is defined by the ANSI/ISO SQL Standard. The SQL standard has been evolving since 1986 and several versions exist. In this manual, “SQL-92” refers to the standard released in 1992, “SQL:1999” refers to the standard released in 1999, and “SQL:2003” refers to the current version of the standard. We use the phrase “the SQL standard” to mean the current version of the SQL Standard at any time.
- MySQL software is Open Source.
Open Source means that it is possible for anyone to use and modify the software. Anybody can download the MySQL software from the Internet and use it without paying anything. If you wish, you may study the source code and change it to suit your needs. The MySQL software uses the GPL (GNU General Public License),http://www.fsf.org/licenses/, to define what you may and may not do with the software in different situations. If you feel uncomfortable with the GPL or need to embed MySQL code into a commercial application, you can buy a commercially licensed version from us. See the MySQL Licensing Overview for more information (http://www.mysql.com/company/legal/licensing/).
- The MySQL Database Server is very fast, reliable, scalable, and easy to use.
If that is what you are looking for, you should give it a try. MySQL Server can run comfortably on a desktop or laptop, alongside your other applications, web servers, and so on, requiring little or no attention. If you dedicate an entire machine to MySQL, you can adjust the settings to take advantage of all the memory, CPU power, and I/O capacity available. MySQL can also scale up to clusters of machines, networked together.
You can find a performance comparison of MySQL Server with other database managers on our benchmark page.
MySQL Server was originally developed to handle large databases much faster than existing solutions and has been successfully used in highly demanding production environments for several years. Although under constant development, MySQL Server today offers a rich and useful set of functions. Its connectivity, speed, and security make MySQL Server highly suited for accessing databases on the Internet.
- MySQL Server works in client/server or embedded systems.
The MySQL Database Software is a client/server system that consists of a multi-threaded SQL server that supports different backends, several different client programs and libraries, administrative tools, and a wide range of application programming interfaces (APIs).
We also provide MySQL Server as an embedded multi-threaded library that you can link into your application to get a smaller, faster, easier-to-manage standalone product.
- A large amount of contributed MySQL software is available.
MySQL Server has a practical set of features developed in close cooperation with our users. It is very likely that your favorite application or language supports the MySQL Database Server.
The official way to pronounce “MySQL” is “My Ess Que Ell” (not “my sequel”), but we do not mind if you pronounce it as “my sequel” or in some other localized way.
Internals and Portability
Written in C and C++.
Tested with a broad range of different compilers.
Works on many different platforms.
For portability, uses CMake in MySQL 5.5 and up. Previous series use GNU Automake, Autoconf, and Libtool.
Tested with Purify (a commercial memory leakage detector) as well as with Valgrind, a GPL tool (http://developer.kde.org/~sewardj/).
Uses multi-layered server design with independent modules.
Designed to be fully multi-threaded using kernel threads, to easily use multiple CPUs if they are available.
Provides transactional and nontransactional storage engines.
Uses very fast B-tree disk tables (MyISAM) with index compression.
Designed to make it relatively easy to add other storage engines. This is useful if you want to provide an SQL interface for an in-house database.
Uses a very fast thread-based memory allocation system.
Executes very fast joins using an optimized nested-loop join.
Implements in-memory hash tables, which are used as temporary tables.
Implements SQL functions using a highly optimized class library that should be as fast as possible. Usually there is no memory allocation at all after query initialization.
Provides the server as a separate program for use in a client/server networked environment, and as a library that can be embedded (linked) into standalone applications. Such applications can be used in isolation or in environments where no network is available.
Data Types
Many data types: signed/unsigned integers 1, 2, 3, 4, and 8 bytes long, FLOAT, DOUBLE, CHAR, VARCHAR, BINARY,VARBINARY, TEXT, BLOB, DATE, TIME, DATETIME, TIMESTAMP, YEAR, SET, ENUM, and OpenGIS spatial types. SeeChapter 11, Data Types.
Fixed-length and variable-length string types.
Statements and Functions
Full operator and function support in the SELECT list and WHERE clause of queries. For example:
mysql> SELECT CONCAT(first_name, ‘ ‘, last_name)
-> FROM citizen
-> WHERE income/dependents > 10000 AND age > 30;
Full support for SQL GROUP BY and ORDER BY clauses. Support for group functions(COUNT(), AVG(), STD(),SUM(), MAX(), MIN(), and GROUP_CONCAT()).
Support for LEFT OUTER JOIN and RIGHT OUTER JOIN with both standard SQL and ODBC syntax.
Support for aliases on tables and columns as required by standard SQL.
Support for DELETE, INSERT, REPLACE, and UPDATE to return the number of rows that were changed (affected), or to return the number of rows matched instead by setting a flag when connecting to the server.
Support for MySQL-specific SHOW statements that retrieve information about databases, storage engines, tables, and indexes. MySQL 5.0 adds support for the INFORMATION_SCHEMA database, implemented according to standard SQL.
An EXPLAIN statement to show how the optimizer resolves a query.
Independence of function names from table or column names. For example, ABS is a valid column name. The only restriction is that for a function call, no spaces are permitted between the function name and the “(” that follows it.
You can refer to tables from different databases in the same statement.
Security
A privilege and password system that is very flexible and secure, and that enables host-based verification.
Password security by encryption of all password traffic when you connect to a server.
Scalability and Limits
Support for large databases. We use MySQL Server with databases that contain 50 million records. We also know of users who use MySQL Server with 200,000 tables and about 5,000,000,000 rows.
Support for up to 64 indexes per table (32 before MySQL 4.1.2). Each index may consist of 1 to 16 columns or parts of columns. The maximum index width is 767 bytes for InnoDB tables, or 1000 for MyISAM; before MySQL 4.1.2, the limit is 500 bytes. An index may use a prefix of a column for CHAR, VARCHAR, BLOB, or TEXT column types.
Connectivity
Clients can connect to MySQL Server using several protocols:
Clients can connect using TCP/IP sockets on any platform.
On Windows systems in the NT family (NT, 2000, XP, 2003, or Vista), clients can connect using named pipes if the server is started with the –enable-named-pipe option. In MySQL 4.1 and higher, Windows servers also support shared-memory connections if started with the –shared-memory option. Clients can connect through shared memory by using the –protocol=memory option.
On Unix systems, clients can connect using Unix domain socket files.
MySQL client programs can be written in many languages. A client library written in C is available for clients written in C or C++, or for any language that provides C bindings.
APIs for C, C++, Eiffel, Java, Perl, PHP, Python, Ruby, and Tcl are available, enabling MySQL clients to be written in many languages.
The Connector/ODBC (MyODBC) interface provides MySQL support for client programs that use ODBC (Open Database Connectivity) connections. For example, you can use MS Access to connect to your MySQL server. Clients can be run on Windows or Unix. Connector/ODBC source is available. All ODBC 2.5 functions are supported, as are many others.
The Connector/J interface provides MySQL support for Java client programs that use JDBC connections. Clients can be run on Windows or Unix. Connector/J source is available.
MySQL Connector/Net enables developers to easily create .NET applications that require secure, high-performance data connectivity with MySQL. It implements the required ADO.NET interfaces and integrates into ADO.NET aware tools. Developers can build applications using their choice of .NET languages. MySQL Connector/Net is a fully managed ADO.NET driver written in 100% pure C#.
Localization
The server can provide error messages to clients in many languages. Full support for several different character sets, including latin1 (cp1252), german, big5, ujis, and more. For example, the Scandinavian characters “å”, “ä” and “ö” are permitted in table and column names. Unicode support is available as of MySQL 4.1.
All data is saved in the chosen character set.
Sorting and comparisons are done according to the chosen character set and collation (using latin1 and Swedish collation by default). It is possible to change this when the MySQL server is started. To see an example of very advanced sorting, look at the Czech sorting code. MySQL Server supports many different character sets that can be specified at compile time and runtime.
As of MySQL 4.1, the server time zone can be changed dynamically, and individual clients can specify their own time zone.
Clients and Tools
MySQL includes several client and utility programs. These include both command-line programs such asmysqldump and mysqladmin, and graphical programs such as MySQL Workbench.
MySQL Server has built-in support for SQL statements to check, optimize, and repair tables. These statements are available from the command line through the mysqlcheck client. MySQL also includes myisamchk, a very fast command-line utility for performing these operations on MyISAM tables.
MySQL programs can be invoked with the –help or -? option to obtain online assistance.
NORMALIZATION
A Database is a collection of interrelated data stored with a minimum of redundancy to serve many applications. The database design is used to group data into a number of tables and minimizes the artificiality embedded in using separate files. The tables are organized to:
- Reduced duplication of data.
- Simplify functions like adding, deleting, modifying data etc..,
- Retrieving data
- Clarity and ease of use
- More information at low cost
Normalization
Normalization is built around the concept of normal forms. A relation is said to be in a particular normal form if it satisfies a certain specified set of constraints on the kind of functional dependencies that could be associated with the relation. The normal forms are used to ensure that various types of anomalies and inconsistencies are not introduced into the database.
First Normal Form:
A relation R is in first normal form if and only if all underlying domains contained atomic values only.
Second Normal Form:
A relation R is said to be in second normal form if and only if it is in first normal form and every non-key attribute is fully dependent on the primary key.
Third Normal Form:
A relation R is said to be in third normal form if and only if it is in second normal form and every non key attribute is non transitively depend on the primary key.
Data Dictionary
| admin | ||||
| Field | Type | Null | Key | Default |
| id | int(11) | NO | PRI | (NULL) |
| UserName | varchar(100) | NO | (NULL) | |
| Password | varchar(100) | NO | (NULL) | |
| updationDate | timestamp | NO | 0000-00-00 00:00:00 |
| tbldepartments | ||||
| Field | Type | Null | Key | Default |
| id | int(11) | NO | PRI | (NULL) |
| DepartmentName | varchar(150) | YES | (NULL) | |
| DepartmentShortName | varchar(100) | NO | (NULL) | |
| DepartmentCode | varchar(50) | YES | (NULL) | |
| CreationDate | timestamp | YES | CURRENT_TIMESTAMP |
| tblemployees | ||||
| Field | Type | Null | Key | Default |
| id | int(11) | NO | PRI | (NULL) |
| EmpId | varchar(100) | NO | (NULL) | |
| FirstName | varchar(150) | NO | (NULL) | |
| LastName | varchar(150) | NO | (NULL) | |
| EmailId | varchar(200) | NO | (NULL) | |
| Password | varchar(180) | NO | (NULL) | |
| Gender | varchar(100) | NO | (NULL) | |
| Dob | varchar(100) | NO | (NULL) | |
| Department | varchar(255) | NO | (NULL) | |
| Address | varchar(255) | NO | (NULL) | |
| City | varchar(200) | NO | (NULL) | |
| Country | varchar(150) | NO | (NULL) | |
| Phonenumber | char(11) | NO | (NULL) | |
| Status | int(1) | NO | (NULL) | |
| RegDate | timestamp | NO | CURRENT_TIMESTAMP |
| tblleaves | ||||
| Field | Type | Null | Key | Default |
| id | int(11) | NO | PRI | (NULL) |
| LeaveType | varchar(110) | NO | (NULL) | |
| ToDate | varchar(120) | NO | (NULL) | |
| FromDate | varchar(120) | NO | (NULL) | |
| Description | mediumtext | NO | (NULL) | |
| PostingDate | timestamp | NO | CURRENT_TIMESTAMP | |
| AdminRemark | mediumtext | YES | (NULL) | |
| AdminRemarkDate | varchar(120) | YES | (NULL) | |
| Status | int(1) | NO | (NULL) | |
| IsRead | int(1) | NO | (NULL) | |
| empid | int(11) | YES | MUL | (NULL) |
| tblleavetype | ||||
| Field | Type | Null | Key | Default |
| id | int(11) | NO | PRI | (NULL) |
| LeaveType | varchar(200) | YES | (NULL) | |
| Description | mediumtext | YES | (NULL) | |
| CreationDate | timestamp | NO | CURRENT_TIMESTAMP |
Introduction to Testing:
Testing is a process, which reveals errors in the program. It is the major quality measure employed during software development. During software development. During testing, the program is executed with a set of test cases and the output of the program for the test cases is evaluated to determine if the program is performing as it is expected to perform.
TESTING IN STRATEGIES
In order to make sure that the system does not have errors, the different levels of testing strategies that are applied at differing phases of software development are:
Unit Testing:
Unit Testing is done on individual modules as they are completed and become executable. It is confined only to the designer’s requirements.
Each module can be tested using the following two Strategies:
Black Box Testing:
In this strategy some test cases are generated as input conditions that fully execute all functional requirements for the program. This testing has been uses to find errors in the following categories:
- Incorrect or missing functions
- Interface errors
- Errors in data structure or external database access
- Performance errors
- Initialization and termination errors.
In this testing only the output is checked for correctness.
The logical flow of the data is not checked.
White Box testing:
In this the test cases are generated on the logic of each module by drawing flow graphs of that module and logical decisions are tested on all the cases. It has been uses to generate the test cases in the following cases:
- Guarantee that all independent paths have been Executed.
- Execute all logical decisions on their true and false Sides.
- Execute all loops at their boundaries and within their operational bounds
- Execute internal data structures to ensure their validity.
Integrating Testing :
Integration testing ensures that software and subsystems work together a whole. It tests the interface of all the modules to make sure that the modules behave properly when integrated together.
System Testing :
Involves in-house testing of the entire system before delivery to the user. It’s aim is to satisfy the user the system meets all requirements of the client’s specifications.
Acceptance Testing :
It is a pre-delivery testing in which entire system is tested at client’s site on real world data to find errors.
Test Approach :
Testing can be done in two ways:
- Bottom up approach
- Top down approach
Bottom up Approach:
Testing can be performed starting from smallest and lowest level modules and proceeding one at a time. For each module in bottom up testing a short program executes the module and provides the needed data so that the module is asked to perform the way it will when embedded with in the larger system. When bottom level modules are tested attention turns to those on the next level that use the lower level ones they are tested individually and then linked with the previously examined lower level modules.
Top down approach:
This type of testing starts from upper level modules. Since the detailed activities usually performed in the lower level routines are not provided stubs are written. A stub is a module shell called by upper level module and that when reached properly will return a message to the calling module indicating that proper interaction occurred. No attempt is made to verify the correctness of the lower level module.
Validation:
The system has been tested and implemented successfully and thus ensured that all the requirements as listed in the software requirements specification are completely fulfilled. In case of erroneous input corresponding error messages are displayed
System Security:
Setting Up Authentication for Web Applications
Introduction:
To configure authentication for a Web Application, use the element of the web.xml deployment descriptor. In this element you define the security realm containing the user credentials, the method of authentication, and the location of resources for authentication.
SECURITY IN SOFTWARE
To set up authentication for Web Applications:
- Open the web.xml deployment descriptor in a text editor or use the Administration Console. Specify the authentication method using the element. The available options are:
BASIC
Basic authentication uses the Web Browser to display a username/password dialog box. This username and password is authenticated against the realm.
FORM
Form-based authentication requires that you return an HTML form containing the username and password. The fields returned from the form elements must be: j_username and j_password, and the action attribute must be j_security_check. Here is an example of the HTML coding for using FORM authentication:
The resource used to generate the HTML form may be an HTML page, a JSP, or a servlet. You define this resource with the
element.
The HTTP session object is created when the login page is served. Therefore, the session.isNew() method returns FALSE when called from pages served after successful authentication.



Leave A Comment
You must be logged in to post a comment.